Many IT leaders at small to mid-sized businesses assume security information event management is something only enterprise companies with dedicated security operations centers can afford and manage. That assumption is costing businesses. A breach at an SMB looks the same as one at a Fortune 500 company, but the recovery rarely does. SIEM technology has matured significantly, and today's cloud-native options make it far more accessible than most decision-makers realize. This article breaks down what SIEM is, how it works, what it costs to get wrong, and how to get it right for your organization.
Table of Contents
- Key Takeaways
- What is security information event management and how it works
- Benefits and key features of SIEM solutions for SMBs
- Deployment options: cloud vs. on-premises SIEM
- Common implementation challenges and success strategies
- How SIEM supports compliance and security posture
- My honest take on SIEM for SMBs
- Ready to get SIEM working for your business?
- FAQ
Key Takeaways
| Point | Details |
|---|---|
| SIEM centralizes security visibility | It collects and correlates logs from across your environment to detect threats in real time. |
| Cloud SIEM is growing fast | The cloud SIEM market is expanding at 12.84% CAGR, making scalable options more accessible for SMBs. |
| Data strategy matters more than volume | Ingesting the right logs beats ingesting all logs. Focused collection prevents data overload. |
| Managed SIEM fills the SOC gap | SMBs without internal security teams can use managed SIEM services to get expert-level monitoring. |
| Tuning is ongoing, not one-time | SIEM rules require continuous refinement to reduce false positives and keep alerts meaningful. |
What is security information event management and how it works
Security information event management, commonly called SIEM, is a technology platform that collects security data from across your IT environment, analyzes it, and generates alerts when something looks wrong. The name itself combines two older disciplines: Security Information Management (SIM), which focuses on long-term log storage and compliance reporting, and Security Event Management (SEM), which handles real-time monitoring and alerting. SIEM brings both together in one platform.
Here is how the process works from start to finish:
- Data collection: The SIEM pulls logs from firewalls, endpoints, servers, cloud services, applications, and identity systems. Every device or service that generates a log is a potential data source.
- Aggregation and normalization: Raw logs come in different formats. The SIEM normalizes them into a consistent structure so they can be compared and analyzed together.
- Event correlation: This is where SIEM earns its value. The platform applies rules and logic to connect related events across different sources. A failed login followed by a successful one from a foreign IP, combined with a large file transfer, becomes a single correlated alert rather than three separate noise events.
- Real-time alerting: When correlated events match a threat pattern, the SIEM fires an alert to your security team or ticketing system.
- Dashboards and reporting: Analysts get a centralized view of security activity, with historical data available for investigations and compliance audits.
Modern SIEM platforms process approximately 500 million security events daily globally, which gives you a sense of the scale these systems are built to handle. Even at the SMB level, you are generating far more security-relevant data than any human team can manually review.
Pro Tip: Start by mapping every system that generates a log in your environment before you evaluate SIEM vendors. That inventory will directly shape your data ingestion strategy and cost estimates.
Benefits and key features of SIEM solutions for SMBs
The practical case for SIEM at an SMB comes down to one reality: threats do not wait for business hours, and most small IT teams cannot monitor everything manually. Here is what a well-deployed SIEM actually delivers:
- Centralized visibility: Instead of logging into five different consoles to check firewall logs, endpoint alerts, and cloud activity separately, your team sees everything in one place.
- Real-time threat detection: SIEM is a frontline necessity for real-time detection of misuse and attacks on IT assets. Waiting for end-of-day log reviews is not a security strategy.
- Faster incident response: When an alert fires, the correlated context is already assembled. Your team spends less time gathering evidence and more time containing the threat.
- Compliance reporting: SIEM logs and reports map directly to frameworks like HIPAA, PCI-DSS, and SOC 2. Audit prep that used to take weeks can be reduced to generating a report.
- Alert prioritization: Raw security tools generate enormous noise. SIEM correlation filters that noise into prioritized, actionable alerts.
- Integration with your existing stack: Modern SIEM platforms connect with endpoint detection tools, identity providers, cloud platforms, and ticketing systems.
One development worth understanding is that modern SIEM now converges security and observability, unifying security telemetry with application performance and infrastructure health data. That means your SIEM is not just catching threats. It is also giving you visibility into whether a performance issue is a technical problem or a security incident in progress.
For SMBs specifically, the reduction in alert fatigue is one of the most underrated benefits. When every alert carries the same urgency, teams stop responding to alerts carefully. SIEM correlation and prioritization fix that.
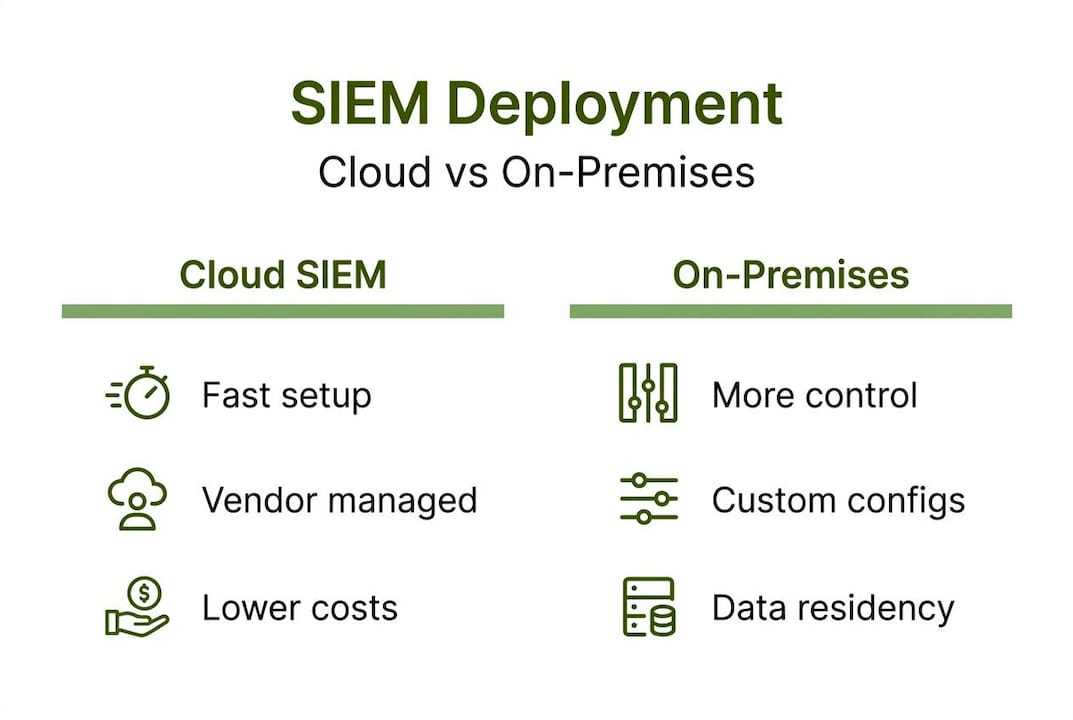
Deployment options: cloud vs. on-premises SIEM
Choosing where your SIEM lives is one of the most consequential decisions you will make. Each model has real trade-offs, and the right answer depends on your team size, budget, and risk tolerance.
| Deployment Model | Pros | Cons |
|---|---|---|
| Cloud SIEM (SaaS) | Fast deployment, vendor-managed scaling, lower upfront cost | Data leaves your perimeter, ongoing subscription cost |
| On-premises SIEM | Full data control, no vendor dependency | High upfront cost, requires dedicated staff to maintain |
| Managed SIEM | Expert monitoring included, no internal SOC needed | Less direct control, dependent on provider quality |
The cloud direction is clear. The cloud SIEM market is growing at 12.84% CAGR as organizations shift infrastructure maintenance and scaling responsibilities to vendors. For an SMB without a dedicated security engineer, that shift makes a lot of sense. You get enterprise-grade detection without hiring a team to keep the platform running.
On-premises SIEM still makes sense in specific scenarios, particularly for organizations with strict data residency requirements or regulated industries where log data cannot leave a controlled environment. The trade-off is real: you own the maintenance, the hardware, the upgrades, and the tuning. That overhead adds up fast.
Managed SIEM is worth serious consideration for most SMBs. The overall SIEM market is growing at 10.3% CAGR through 2029, driven largely by demand for managed services from organizations that lack internal security operations centers. A managed SIEM provider combines the technology with expert human monitoring, which is something a SaaS subscription alone does not give you.
Pro Tip: When evaluating cloud SIEM vendors, ask specifically how they charge for data ingestion. Some bill by volume, which can create unpredictable monthly costs if your log volume spikes during an incident or a new integration.
Understanding your security responsibility boundaries before selecting a deployment model will save you from discovering gaps after the contract is signed.
Common implementation challenges and success strategies
Most SIEM deployments that fail do not fail because the technology is bad. They fail because of predictable, avoidable mistakes. Here is what to watch for and how to handle each one.
-
Over-collecting data from the start. SIEM vendors often charge by data ingestion volume, and unmanaged collection creates unpredictable costs. Worse, collecting massive log volumes without prioritization leads to poor threat detection outcomes. Start with your highest-value sources: authentication logs, firewall logs, and endpoint activity.
-
Skipping rule tuning after go-live. Out-of-the-box SIEM rules are a starting point, not a finished product. Every environment is different, and default rules will generate false positives that erode your team's trust in the system. Plan for at least 30 to 60 days of active tuning after deployment.
-
Ignoring operational overhead in the cost model. Choosing SIEM without weighing operational overhead and architecture trade-offs leads to wasted budgets and detection gaps. The license fee is rarely the biggest cost. Staff time for tuning, investigation, and maintenance often exceeds it.
-
Treating detection rules as static configurations. Detection-as-Code for SIEM enables version-controlled, testable, and reversible rules. When you manage rules the same way developers manage code, you get fewer errors, easier rollbacks, and better team collaboration.
-
Underestimating staff training requirements. A SIEM is only as good as the analysts interpreting its alerts. Your team needs to understand what the platform is telling them and how to act on it.
Pro Tip: Build your initial detection rule set around your top five threat scenarios, not around everything the vendor's default library covers. Focused rules produce focused alerts, and focused alerts get acted on.
How SIEM supports compliance and security posture
For SMBs operating under regulatory requirements, SIEM is not just a security tool. It is a compliance asset. Here is how it supports both:
- Log retention and audit trails: SIEM platforms store logs for defined retention periods, which satisfies requirements under HIPAA, PCI-DSS, SOC 2, and other frameworks. When an auditor asks for six months of authentication logs, you pull a report rather than scrambling through individual system exports.
- Automated compliance reporting: Most enterprise SIEM platforms include pre-built report templates mapped to major compliance frameworks. That removes significant manual work from your audit preparation cycle.
- Faster investigations: Centralized SIEM dashboards increase the speed of threat detection and remediation. When a security incident occurs, the correlated data is already in one place, which cuts investigation time significantly.
- Integration with SOAR and XDR: Modern security stacks often pair SIEM with Security Orchestration, Automation and Response (SOAR) tools and Extended Detection and Response (XDR) platforms. SIEM provides the data and detection layer. SOAR automates the response workflows. XDR extends visibility across endpoints, network, and cloud in a unified way.
The connection between SIEM data and broader IT health is also worth noting. SIEM as a proactive tool integrates security telemetry with operational data to improve both threat detection and IT visibility. That means your compliance reporting and your security posture benefit from the same investment.
My honest take on SIEM for SMBs
I have worked with enough small and mid-sized businesses to know that SIEM conversations often start in the wrong place. Decision-makers focus on the platform features and the price tag, and they underestimate what it actually takes to run the thing well.
In my experience, the biggest SIEM failures I have seen were not technology failures. They were operational failures. A team deploys a capable platform, leaves the default rules in place, gets buried in false positives within 60 days, and stops trusting the alerts. At that point, the SIEM is running but not protecting anyone.
What I have found actually works is treating SIEM like a program, not a product. You buy it, you configure it, and then you commit to managing it the way you manage any other critical system. That means scheduled rule reviews, documented tuning decisions, and someone accountable for alert quality. The Detection-as-Code approach is not just a technical concept. It is a discipline that makes SIEM sustainable.
For most SMBs I work with, cloud-native or managed SIEM is the right call. Not because on-premises is inherently bad, but because the operational overhead of running your own SIEM infrastructure is a real burden that most small IT teams cannot absorb without sacrificing something else. Managed services let you get the monitoring without building a mini-SOC.
The long game matters too. Your data strategy today determines how useful your SIEM is in two years. Start narrow, tune aggressively, and expand your data sources as your team's confidence grows.
— Greg
Ready to get SIEM working for your business?
Understanding SIEM is one thing. Deploying and managing it effectively is another challenge entirely, especially when your IT team is already stretched thin. That is where Ventisconsulting comes in.

Ventisconsulting works with small and mid-sized businesses in Pittsburgh and the surrounding region to deploy, configure, and manage security monitoring solutions that fit your actual environment and budget. From initial security assessments to ongoing managed monitoring, the team at Ventisconsulting handles the operational complexity so your team can focus on running the business. You get expert-level security coverage without building a security operations center from scratch. Explore managed IT services from Ventisconsulting and see what a properly supported SIEM program looks like for an SMB like yours. Or start with a security questionnaire to identify where your current gaps are.
FAQ
What is SIEM in simple terms?
SIEM stands for Security Information and Event Management. It is a platform that collects logs from across your IT environment, correlates them to detect threats, and generates alerts for your security team to act on.
How does SIEM work for a small business?
SIEM pulls security data from your firewalls, endpoints, cloud services, and applications, then applies correlation rules to identify suspicious activity. For SMBs, cloud-based or managed SIEM options reduce the infrastructure and staffing burden significantly.
What is the difference between cloud SIEM and on-premises SIEM?
Cloud SIEM is hosted and maintained by the vendor, offering faster deployment and lower upfront costs. On-premises SIEM gives you full data control but requires dedicated staff and hardware to operate and maintain.
Why do SIEM implementations fail?
Most SIEM failures come from over-collecting data, skipping ongoing rule tuning, and underestimating operational overhead. Starting with high-value log sources and committing to active tuning after deployment are the two most effective ways to avoid those pitfalls.
Does SIEM help with compliance reporting?
Yes. SIEM platforms store logs for defined retention periods and generate pre-built compliance reports mapped to frameworks like HIPAA, PCI-DSS, and SOC 2, which reduces audit preparation time significantly.
